Remote work has transformed the way modern companies operate, giving teams the freedom to collaborate from anywhere in the world. Yet with this flexibility comes a pressing challenge: protecting sensitive data outside the traditional office perimeter. Cyber threats, unsecured public Wi-Fi, varied home network configurations, and cross-border compliance issues all create vulnerabilities. One powerful but often misunderstood solution to these challenges is the proxy server.
TLDR: Proxy servers act as intermediaries between remote employees and the internet, helping mask IP addresses, encrypt traffic, and enforce security policies. They reduce exposure to cyber threats and enable secure access to company resources from anywhere. For distributed teams, proxies strengthen privacy, centralize traffic control, and improve compliance. When implemented correctly, they become a critical layer in a modern remote security strategy.
As remote teams continue to grow, understanding how proxy servers improve privacy is essential for organizations that prioritize both security and productivity. Let’s explore how they work and why they are such a valuable addition to remote infrastructure.
What Is a Proxy Server?
At its core, a proxy server acts as an intermediary between a user’s device and the internet. Instead of connecting directly to a website or cloud service, the user’s request first travels to the proxy. The proxy then forwards the request to its destination and returns the response to the user.
This extra step may seem simple, but it provides multiple layers of protection and control.
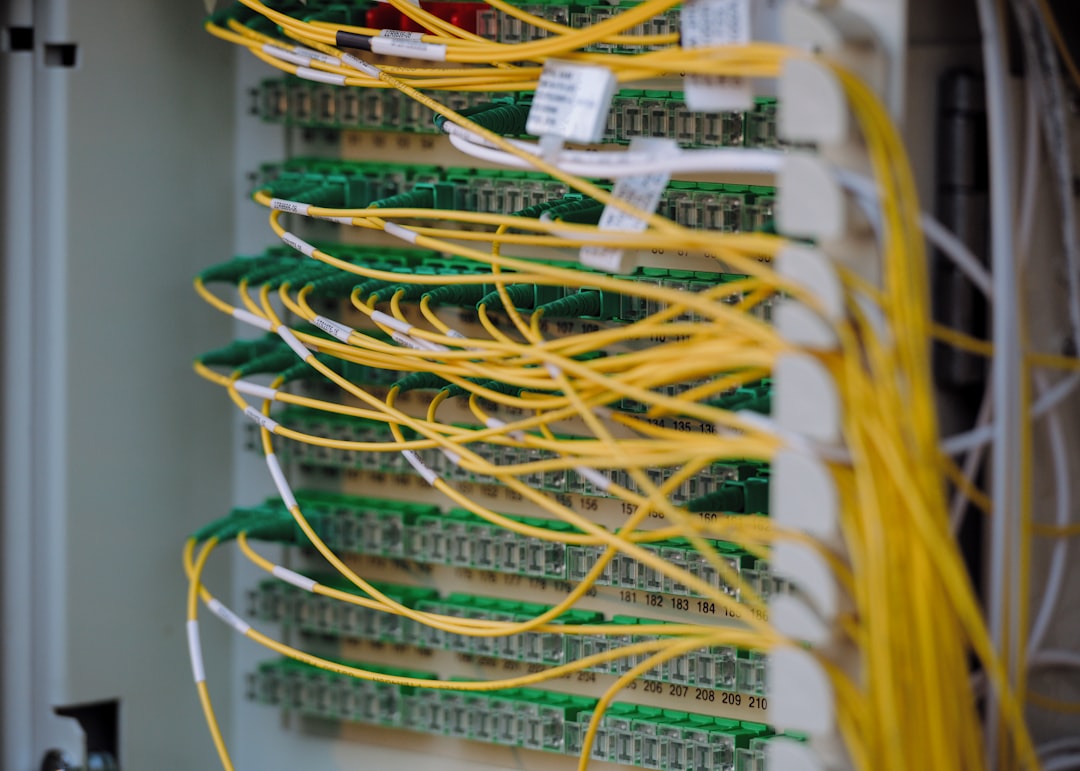
Image not found in postmetaThere are several types of proxy servers commonly used by remote teams:
- Forward proxies – Sit between users and the internet, masking user identities.
- Reverse proxies – Protect company servers by filtering incoming traffic.
- Transparent proxies – Operate without user configuration, often used for monitoring.
- Anonymous or elite proxies – Hide user IP information more completely.
Each of these types can play a role in strengthening privacy for distributed workforces.
1. Masking IP Addresses and Location Data
One of the most immediate privacy benefits of a proxy server is IP address masking. Every device connected to the internet has a unique IP address that reveals approximate geographic location and network information. For remote workers, this can expose:
- Home locations
- Internet service provider details
- Network infrastructure information
By routing traffic through a proxy server, the external website sees the proxy’s IP address instead of the employee’s. This shields personal location details and minimizes the risk of targeted attacks.
Example: A finance employee accessing sensitive cloud accounting software from a home network is less exposed when their real IP address is hidden behind a secure corporate proxy.
2. Encrypting Outbound Traffic
Privacy is not just about hiding identity — it is also about protecting the content of communication. Many modern proxy solutions support SSL encryption, ensuring that data traveling between remote employees and company systems cannot be easily intercepted.
This is especially important when team members use:
- Public Wi-Fi in airports or cafés
- Shared coworking spaces
- Home networks with limited security oversight
Without encryption, cybercriminals may use packet sniffing tools to eavesdrop on sensitive communications. A properly configured secure proxy creates an added encrypted tunnel, dramatically lowering the risk of interception.
3. Centralized Control and Monitoring
Managing a remote workforce can create blind spots for IT departments. Proxy servers help solve this by centralizing traffic management.
Organizations can configure proxies to:
- Block malicious websites
- Restrict access to risky platforms
- Monitor unusual traffic behavior
- Log activity for auditing purposes
Rather than relying on each employee’s individual device security, companies maintain policy enforcement at the network level. This reduces the likelihood of compromised endpoints exposing the wider organization.

For compliance-heavy industries such as healthcare or finance, this centralized oversight is especially valuable. It provides accountability and audit trails, both critical components of regulatory compliance frameworks.
4. Protecting Against Cyber Threats
Remote teams are common targets for phishing attacks, malware distribution, and ransomware campaigns. Proxy servers act as a first line of defense by filtering harmful content before it reaches employee devices.
Advanced proxies integrate with threat intelligence databases to:
- Detect known malicious domains
- Block suspicious downloads
- Prevent communication with command and control servers
This proactive filtering prevents many threats from ever reaching the user. In effect, the proxy acts as a security gatekeeper.
5. Enabling Safe Access to Geo-Restricted Resources
Remote teams frequently span continents. However, certain services, pricing models, or research resources may be regionally restricted. Secure proxy servers allow employees to connect through approved geographic endpoints without exposing their personal networks.
Unlike risky public proxy services, enterprise-grade solutions:
- Offer authenticated access
- Encrypt traffic fully
- Maintain compliance standards
This enables legitimate business operations while balancing security and privacy.
Proxy Servers vs VPNs for Remote Privacy
While proxy servers and VPNs are often mentioned together, they serve slightly different roles. Below is a simplified comparison to clarify how proxies stand out.
| Feature | Proxy Server | VPN |
|---|---|---|
| IP Masking | Yes | Yes |
| Encrypts All Device Traffic | Sometimes (depends on configuration) | Yes |
| Application-Level Control | Strong | Limited |
| Traffic Filtering | Advanced content filtering | Minimal native filtering |
| Performance Impact | Generally lower | Can be higher due to full encryption |
In many organizations, proxies and VPNs are used together to create layered protection. However, proxy servers excel in traffic control, visibility, and fine-grained policy enforcement — making them particularly useful for remote teams.
6. Enhancing Privacy Without Sacrificing Performance
One common concern with security tools is speed reduction. Proxies can actually improve performance through caching mechanisms.
When multiple remote employees access the same cloud-based resources, the proxy can:
- Store copies of frequently requested files
- Reduce redundant traffic
- Optimize bandwidth usage
By minimizing direct external calls, the organization benefits from both improved speed and enhanced privacy controls.
7. Supporting Compliance and Data Governance
Data privacy regulations such as GDPR, HIPAA, and SOC 2 require organizations to demonstrate strong data protection practices. Proxy servers contribute to compliance by:
- Providing detailed access logs
- Blocking unauthorized data transmissions
- Restricting uploads to unsanctioned services
For remote teams handling personally identifiable information or health records, this infrastructure becomes indispensable.
Moreover, granular access policies ensure that employees only access the systems relevant to their roles — reinforcing the principle of least privilege.
Best Practices for Implementing Proxy Servers in Remote Teams
Simply deploying a proxy is not enough. To maximize privacy benefits, organizations should follow these best practices:
- Use authenticated proxy access to prevent misuse.
- Combine proxies with endpoint security tools for layered defense.
- Regularly update filtering rules to address emerging threats.
- Educate remote employees on secure browsing practices.
- Monitor logs responsibly while respecting employee privacy boundaries.
Balancing privacy with oversight is key. Proxy deployment should enhance protection without creating unnecessary intrusions into employee autonomy.
The Future of Proxy Use in Distributed Workforces
As hybrid and fully remote models become permanent fixtures of the business landscape, proxy technology continues to evolve. Modern cloud-based proxy solutions integrate with zero trust architecture, identity management platforms, and artificial intelligence-driven threat detection.
Instead of relying on a fixed office perimeter, companies now secure the user, device, and application — wherever they are. Proxy servers serve as intelligent traffic managers within this broader ecosystem.
With cyber threats growing more sophisticated and privacy expectations increasing, proxy servers are no longer optional for many remote-first companies. They represent a practical, scalable, and highly adaptable solution to the privacy challenges of distributed work.
Conclusion
Remote work brings unmatched flexibility, but it also expands the attack surface for modern organizations. Proxy servers improve privacy for remote teams by masking IP addresses, encrypting traffic, filtering malicious content, and centralizing policy enforcement. Combined with other cybersecurity measures, they create a resilient digital shield that protects both individuals and corporate assets.
In a world where teams collaborate across time zones and networks vary in quality and security, proxy servers provide consistency, control, and peace of mind — all without slowing productivity. For organizations looking to build a secure remote infrastructure, implementing proxy technology is not just smart — it is essential.
